
Hadi Zeinaldeen
Published On: 15 May 2019

Crashing web/mobile clients by bypassing comment character limit
Rate Limits
Linkedin | Web
---
UNDEFINED VALIDDescription
Intercepting the request and adding a huge amount of text to it and then forwarding it will bypass the character count limit, causing client devices to crash while trying to load the comment.
Impact
By placing a really large comment on someone's post (potentially even big accounts like the official linkedin account followed by millions of users), an attacker can disable access to this post, and any news-feed this post appears in.
Reproduction Steps
Step
1
Step
2
Step
3
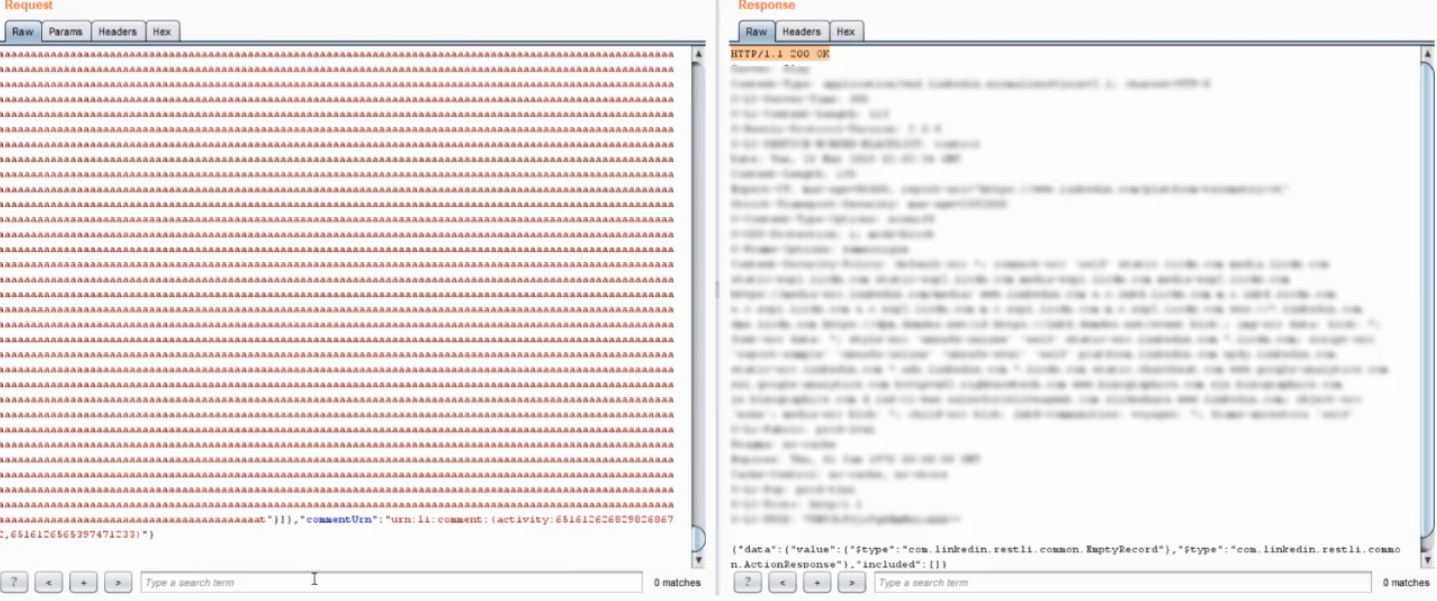
Edit the request "newCommentText":{"values":[{"value":"my comment"}]} and place a really large text in place of the comment value, then forward the request.
Timeline
VALID


